As one of the most rigorous cybersecurity-based certification exams, the Offensive Security Certified Professional (OSCP) is designed to demonstrate the InfoSec professionals’ highest level of penetration testing competences, as well as their knowledge in concepts of cyber defense.
Those who obtain the OSCP certification can be considered the go-to individuals in cybersecurity, as they are well-versed in offensive strategies and hacking techniques used in pentesting. To become an OSCP expert, Alexandru Colțuneac, Zitec’s Security Engineer, put his problem-solving and analytical thinking skills to the test when he enrolled in the biggest exam of his career.
After 48 hours of intensive analysis of system flaws and configuration mistakes, Alex explained to us what an OSCP examination means and why it is worth going through such a thorough practical hacking exercise.
OSCP - the ethical hacking certification that validates a professional’s penetration testing skills
The Offensive Security Certified Professional or OSCP is a professionally-recognized certification, awarded to anyone who successfully finishes a 24-hour practical exercise, followed by another 24-hour analysis report.
A security and IT professional accredited with this certification demonstrates that they are knowledgeable in penetration testing and attack methodologies used against infrastructure, systems, and devices. OSCP specialists also have expertise in identifying known or unknown vulnerabilities, using tools inherent in the Kali Linux distribution - an open-source Linux distribution that allows experts to assess the security of their own systems.
Once Offensive Security (OffSec) rewards the OSCP, the security holder doesn’t need to renew it or requalify. Yet, all those who engage in unethical practices during or after the exam, or even divulge the test materials will have their certification revoked. The OffSec examiners are entitled to ban those who bend the rules from any Offensive Security courses or offerings.
OffSec doesn’t report how many experts are OSCP certified or the exam success rate.
Let’s meet Alexandru Colțuneac and learn about his journey of becoming an OSCP-certified expert
As we have laid the foundation of what OSCP is, Alexandru Colțuneac, Zitec’s OSCP expert, shared his experience before and during the exam, as well as what it means to be part of the Security & Data Protection team.
Origins of interest: Unraveling the roots of Software Security passion
Alex, you are currently a Senior Security Engineer at Zitec, but how exactly did your interest in software security begin?
“Indeed, I’ve been in the Security team for a little over 2 years as a Senior Security Engineer, but cybersecurity has always been my passion. I discovered this field in high school, when I started my career as an ethical hacker. Later, I enrolled in the Computer Science department at Babes-Bolyai University in Cluj.
My security story began many years ago, in 2012, when I found a post on a hacker forum about someone who had found and reported a vulnerability in Yahoo’s system. It was fascinating for me, the kid at that time, to know that someday I could, as well, make a contribution for a reputable company, a giant in IT such as Yahoo. Actually, I started my professional career as a bug hunter, looking for vulnerabilities for different companies like Facebook and Google. In the following year, Facebook even listed me on a special page that points out all the hackers who found and reported a security issue on their sites.
But although I live in Cluj, I work remotely in Bucharest. I got into contact with Zitec through a colleague, Dorin Huseraș, with whom I had previously worked in another company. I was initially reluctant about this new job opening in the Security department because I was attracted to the idea of working on my own as a freelancer. But Dorin managed to convince me to join the team.
I soon learned that Zitec is the type of company that invests in both its customers and team. One of the benefits here for any employee is the learning opportunities, such as obtaining professional certifications. In May 2023, I got this opportunity myself, when I obtained my first certification, and in fact, the most important for my career: OSCP - Offensive Security Certified Professional.”
The value of the OSCP certification: A detailed insight
You mentioned OSCP as being the most important certification for you. Why is it so and how does it benefit the ones who work with an OSCP expert?
“OSCP is a well-regarded certification in the cybersecurity field because it attests not only the high level of technical hacking competences that you possess, but it also demonstrates that the certified person has strong reporting skills and understanding of what goes behind any vulnerability.
For companies and partners that work with any professional in the security industry, having this certification in your portfolio is very important because OSCP is difficult to obtain and is proof of a higher degree of security and professionalism in pentest than any other certifications. So our partners have the certainty that they are working with someone whose level of knowledge has been recognized by a major security entity.”
Learning for OSCP: An introspective exploration
Tell us about your learning experience. How did you prepare for OSCP?
“The OSCP certification is not something we can study for overnight. But OffSec offers us the possibility to buy their course - a PDF coursebook with all the topics that might appear on the exam. In addition, I had access to explanatory videos and a virtual lab with several servers similar to the ones in the exam.
As far as the learning period is concerned, I wouldn’t say that there is necessarily a specific time frame because the learning experience varies from person to person. For instance, I spent 1 month learning, more or less, but that differs from person to person. I admit, though, that my previous experience, the work I do at Zitec, the hacking activities conducted in the past, and the course helped me a lot to acquire or remember some basic technical skills.
I noticed that Offensive Security recently added a new chapter: the Active Directory (AD) pentesting. This chapter focuses on attack methods and security testing in AD infrastructures, meaning in a company’s internal computer networks where all the employees’ data is stored. So this was something new I focused my attention on.
However, to make my learning experience easier, I approached this exam in a very structured way. So I created a virtual notebook with all the insights I found in the course. I also searched the internet for such “cheat sheets” from other OSCP-certified experts. This was very useful during the exam because I had at my disposal all the necessary information regarding a specific command or tool. Also, I dedicated a good part of my preparation time to hacking machines on the official OSCP laboratories and on HackTheBox platform.
Interestingly enough, ChatGPT was a good way to find answers regarding some of my technical questions about different technologies, the Kerberos protocol and the Active Directory vulnerabilities, for instance. I learned how to write good prompts so that I would receive valuable answers. In addition to all this, I had huge support and encouragement from my team, which mattered immensely."
The Offensive Security platform has a "Reviews" section that allows OSCP-certified people to share their experiences. Here is what another candidate says about their OSCP endeavor:
The OSCP certification was an arduous journey, but well worth the feeling of self accomplishment after completing it. It taught me a different way of thinking, patience, and most importantly...to look closer and think differently. Well worth every second of lab time!
Examining the challenge: The OSCP exam experience
How difficult was the exam for you?
“This exam is challenging, but I wanted to take this test because for me, with a practical certification as OSCP, I can better demonstrate my skills. Being a practical exam, the test has no questions. The only guidelines were that I needed to hack 6 servers. It's an entire process: scanning network ports, looking for open services, analyzing specific or non-specific vulnerabilities. Basically I was given some IP addresses and I had to apply everything I had learned in the course up until the final stage when I gained access to the server and I became the most privileged user/administrator.
Offensive Security’s rules are very strict: everything is being closely monitored during the exam, from the device you log in to every corner of your room. A funny situation during this process with OSCP was that I couldn't sleep the night before the exam. As I was mentally ready to stay awake for another 24 hours and start the test, the examiner saw an unused, unplugged monitor. So he asked me to dismantle it completely, even if it was attached with screws to my desk. It seems funny to me now, but that morning the adrenaline kicked in so fast. You don't really have time to think about the experience itself because you're so focused.
What I realized - and this is a piece of advice I can give to those who want to apply for OSCP - is not to overthink. At one particular moment I got stuck and I couldn’t figure out the solution. 5 hours later I needed a break and out of a sudden, in that moment of disconnection, the solution came right away. And guess what, it was extremely simple. The fact is that there was no need for overcomplicated scenarios; I just needed to take everything step by step because the solution was in front of me. This is something I learned during the exam.”
Role in Focus: A Day in the Life of a Senior Security Engineer at Zitec
What does it mean to be a Senior Security Engineer in the Security & Data Protection team at Zitec?
“When I joined Zitec, I was the third member of the team. Subsequently, the team has grown and we even have people in the security internship program, which I coordinate. We are a relatively small but united team, able to develop very close relationships with our clients. Our portfolio includes big players in both the Romanian and international market: Sameday, Flip, Untold or Beko to name a few.
A Security Engineer’s tasks vary from performing security testing on web applications, mobile applications or IT infrastructures, finding security issues, to developing and maintaining the secure SDLC (Software Development Lifecycle). I audit many source codes, I'm involved in research, risk management, and security consulting. For the security internship, I create the program, I monitor our colleagues’ development, or I correct different papers and reports. There is no room for boredom.”
The Joy of the Job: Finding Fulfillment in the Security Team
What do you like most about working in the Security team?
“I think the biggest benefit is that I have had the opportunity to learn and broaden my knowledge. I have learned here the importance of collaborative work and relying on my colleagues when I lack certain information.
On the technical side, being more involved in the software development area, and seeing how and why vulnerabilities occur, made me understand what developers or product teams need to increase the security of the applications they develop.
Our role as a security team extends beyond interventions and support; we serve as proactive cybersecurity advocates. This is why organizations require a dedicated team, consistently engaged in security projects, to champion cybersecurity initiatives and foster a culture of security awareness across all product teams and developers.”
Looking Ahead: Alexandru's Future Aspirations
What is next for you?
“Firstly, I want to practice as much as possible what I learned in the OSCP certification. Obviously, I want to work my way to other certifications in cybersecurity, but I am thinking of widening my areas of interest. Maybe towards the cloud or management field, with certifications like CISSP.
CISSP can perhaps be considered the Golden Standard in cybersecurity and is aimed at those who want to become cybersecurity consultants. It gives you the opportunity to learn and gain knowledge in several areas: risk, organization, architecture. Basically, it offers a holistic view of security, not just a niched field like penetration testing.”
OSCP vs. other certifications
OSCP is often compared to other certifications like CEH (Certified Ethical Hacker), but each certification has its own scope of practicability.
- CEH consists of a grid exam that lasts 3 hours and is an exam that takes the applicant through a lot of theoretical topics. It requires a certain level of knowledge, but it focuses less on hands-on labs. CEH can be considered more of an entry-level certification than OSCP.
- While CEH validates the ability to think or act like malicious hackers, OSCP highly focuses on penetration testing using Kali Linux. This is aimed at more experienced information security professionals who are able to enumerate machines, identify vulnerabilities, and develop all kinds of solutions.
Testing technical abilities within a fierce 48h live OSCP exam
One of the toughest certifications that can be obtained in the cybersecurity industry, OSCP is a hands-on exam that lasts 48 hours in total.
| Question type |
Hands-on performance-based |
| Exam duration |
24 hours practical exercise + 24 hours reporting |
| Scoring |
70/100 |
| Recommended experience |
Linux, TCP/IP, and BASH scripting with Python or PERL |
| Required experience |
None |
| Exam materials |
Penetration Testing with Kali Linux (PWK-PEN-200) course |
24 hours are allocated to hack into 6 servers from a virtual lab environment; more specifically from a private network through which the candidate connects from their own laptop. Although the lab exam mimics a penetration test, the OffSec expert examines the technical skills needed for offensive white hat hacking, as well as the perseverance and time management abilities. In addition, the exam aims to test candidates’ understanding of TCP/IP networking, their Windows and Linux administration experience, and basic BASH or Python scripting.
OffSec has very stringent rules in regards to the tools, techniques or any electronic devices that can be used during the first phase of the exam. This is why the exam lab period is virtually proctored. The supervisor oversees everything in the exam workstation with screen sharing, chat, and webcam, without audio.
The scoring is quite simple: there are 3 servers with 2 levels of access: as a basic user or as an administrator. 10 points are rewarded for each access, hence, 20 points maximum per server. Besides these, the knowledge in the Active Directory (AD) infrastructure is tested. 3 AD servers must be analyzed for vulnerabilities. To pass, 70/100 points must be obtained.
If the score needed to compromise those servers is attained in the first phase, then another 24-hour period is allocated to create a professional security report. This penetration test report needs to include all the effort made during the exam: the steps taken, the exploitation process, commands issued, and output.
This test has a worldwide reputation for being difficult, and so say other people who have taken it:
Offensive security has a reputation for difficult but good certifications. The penetration testing with Kali/Offensive Security Certified Professional course/certificate lived up to this reputation. Extremely good.
The OSCP test preparation PEN-200 course
To be eligible for the OSCP certification, Offensive Security requires candidates to complete the “Penetration Testing with Kali Linux (PWK-PEN-200)” course. This course is offered exclusively through Offensive Security and is available in two formats: either self-paced or instructor-led.
This test preparation includes both traditional course materials, as well as hands-on simulations through 5 test machines. OffSec provides several topics for further study:
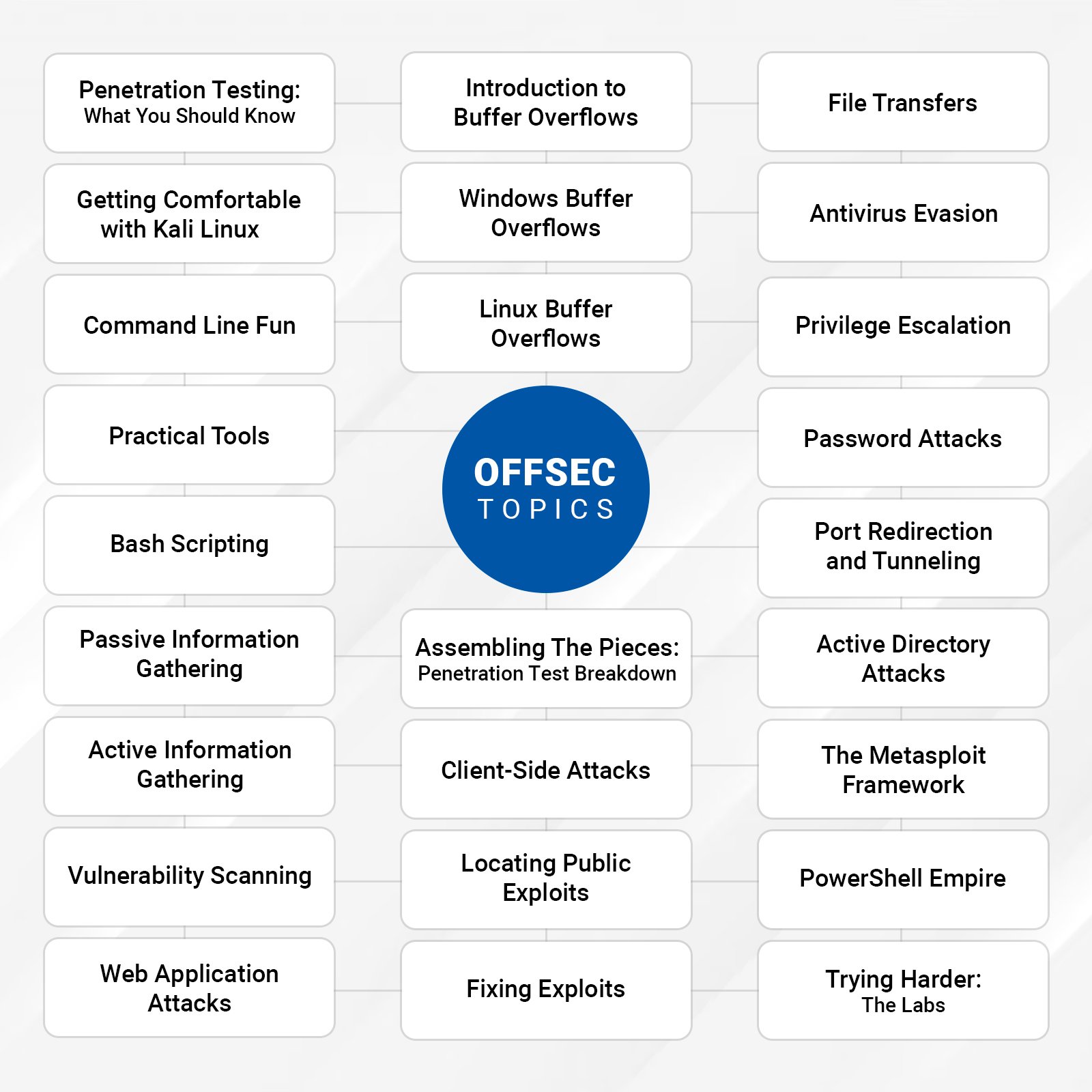
Topics provided by OffSec for further exam study. Source
Therefore, even though someone doesn’t have previous experience in hacking, but still wants to take the certification, the advantage here is that by reading, watching videos, and doing practical things they can develop the necessary competences.
OSCP - the sought-after certification within the penetration testing field
OSCP is extremely important not only for its unique exam that validates professionals’ theoretical and practical abilities, but also for the added value to the corporate technical know-how:
- international recognition in cybersecurity
- expertise in penetration testing and information-gathering techniques
- vulnerability exploitation in various operating systems, services, and protocols
- writing and correcting exploits for the penetration testing process
- problem-solving and lateral thinking skills
- conducting remote or local privilege escalation and client attack
- strengthening the business’ service portfolio
If you want to work with an experienced Security team, accredited in OSCP and other worldwide-recognized certifications, contact us.





.webp)

